Innovative Quantum Approaches Reshaping the Landscape of Cryptographic Security
The Quantum Computing Revolution
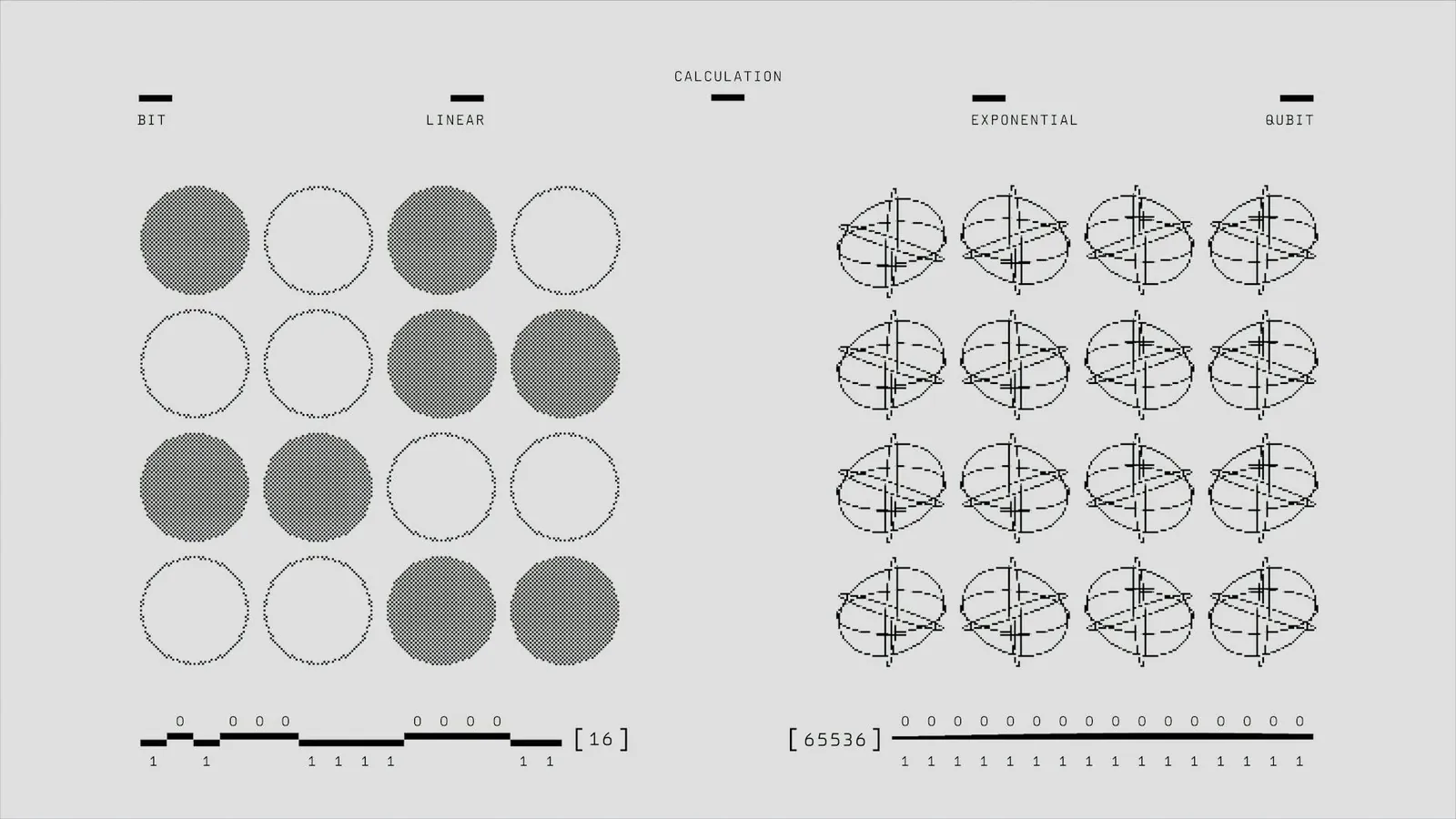
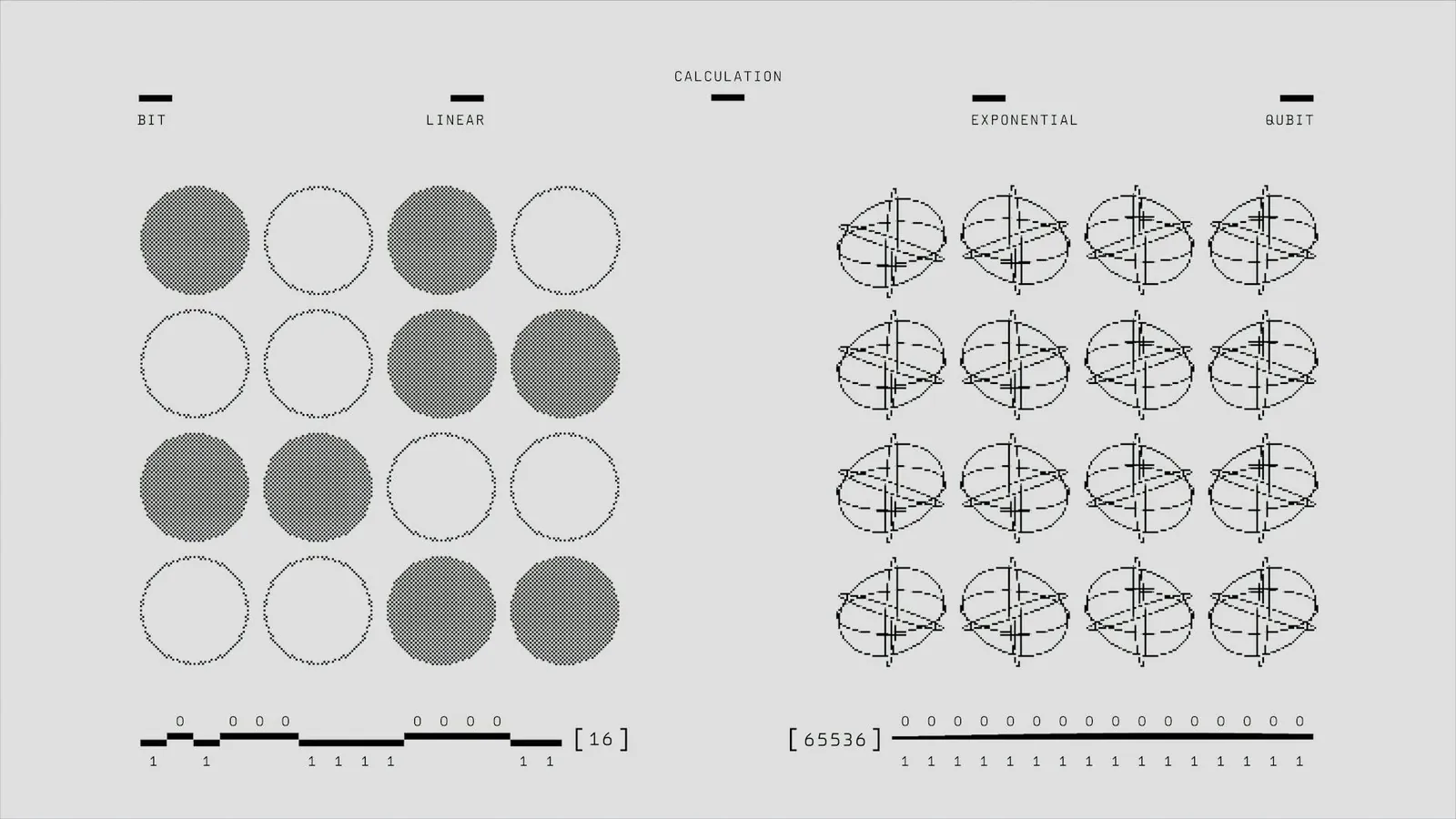
Quantum computing has been a topic of intense interest and research for decades. As traditional computers approach the limits of Moore's Law, quantum computing offers a paradigm shift in processing power and capability.
The Implications for Cryptography
The implications of quantum computing for cryptography are profound. Modern cryptographic systems like RSA and ECC (Elliptic Curve Cryptography) rely on the difficulty of factorizing large numbers or solving discrete logarithm problems, tasks that would take classical computers millions of years to solve. However, quantum algorithms like Shor's algorithm threaten to render these encryption methods obsolete by solving these problems exponentially faster.
Shor's Algorithm: A Game Changer
Developed by mathematician Peter Shor in 1994, Shor's algorithm fundamentally changes how we perceive the security of current cryptographic systems. On a sufficiently powerful quantum computer, Shor's algorithm can efficiently factorize large integers, thus breaking the security of widely used cryptosystems.
Case Study: Breaking RSA Encryption
RSA encryption, a cornerstone of digital security, is based on the difficulty of factoring large prime numbers. Shor's algorithm, running on a theoretical quantum computer with several thousand qubits, could factorize a 2048-bit number in hours, whereas classical computers would need millennia. Researchers have already demonstrated the capability of this algorithm on small numbers using rudimentary quantum processors.
Quantum Key Distribution: An Emerging Solution
As quantum computing poses significant risks to traditional cryptography, scientists are exploring quantum cryptography as a countermeasure. Quantum Key Distribution (QKD) leverages the principles of quantum mechanics to ensure secure communication.
In QKD protocols like BB84, secure keys are generated using quantum properties such as photon polarization. The no-cloning theorem ensures that any attempt at interception alters the system state, revealing eavesdroppers and ensuring key security.
Real-world Applications and Challenges
Numerous companies and research institutions are investing in QKD technology. For example, China has launched a quantum satellite named Micius to facilitate long-distance QKD. However, the high cost and infrastructure requirements pose significant challenges for widespread adoption.
- Cost: Implementing QKD systems requires sophisticated equipment, making it economically feasible primarily for critical sectors like defense and finance.
- Infrastructure: Establishing optical fibers or satellite links for quantum communication can be technically demanding.
Post-Quantum Cryptography: Preparing for the Quantum Era
In anticipation of powerful quantum computers, researchers are developing post-quantum cryptographic algorithms designed to be resistant to both classical and quantum attacks.
NIST's Call for Post-Quantum Standards
The National Institute of Standards and Technology (NIST) is spearheading efforts to standardize post-quantum cryptography. The initiative involves evaluating algorithms that maintain security against adversaries equipped with quantum computers.
Leading contenders in this field include lattice-based cryptography, hash-based signatures, and multivariate polynomial equations. These approaches focus on mathematical problems believed to be hard even for quantum computers.
Concrete Example: Lattice-Based Cryptography
Lattice-based cryptography is based on problems related to integer lattices. The hardness of lattice problems is well-suited for both key exchange and encryption schemes. This method not only provides strong security assurances but is also efficient enough for practical use.
Conclusion: Navigating the Future
The advent of quantum computing marks a significant milestone in the evolution of technology. While it poses challenges to existing cryptographic paradigms, it also provides novel solutions through quantum-enhanced security techniques.
The next decade will likely see a gradual transition as governments and industries adapt to these changes. Investing in research and development, promoting standards for post-quantum cryptography, and increasing collaboration between academia and industry will be pivotal in shaping a secure digital future.
 FreshReads
FreshReads